In the dim and distant past (2 years ago) - i wrote up a post here http://dbaharrison.blogspot.com/2016/11/linux-in-azure-single-sign-on.html talking about how you could authenticate users in linux against AAD for a nicer user management experience - this worked pretty well but wasn't perfect.
It now seems that Microsoft have done this themselves and made the whole thing a lot slicker.
The benefits of the new method are:
Access (including admin access) can be granted directly through the portal - no messing with sudo config on servers.
Reporting on who has access as well as all identity management can also be done from the portal
So lets see how this is configured - first up we need to enable an extension from Microsoft - this currently can't be done from the GUI portal and must be done via one of the command line options - the below is taken from the MS docs and shows doing it with the azure cli -
az vm extension set \
--publisher Microsoft.Azure.ActiveDirectory.LinuxSSH \
--name AADLoginForLinux \
--resource-group myResourceGroup \
--vm-name myVM
Once that extension is installed you are then able to make use of the functionality - if the extension is working fine you should see this status on the extensions page in the portal for AADLoginForLinux
To now add users to be able to login to linux you navigate to the IAM blade in the portal for that VM - from there there are 2 new roles that are grantable to let you login
Virtual Machine User Login (let's you log in to linux as normal user)
Virtual Machine Administrator Login (let's you login and sudo to root)
They are slightly confusingly named i think as the name implies this works for any VM type - but this does not work for windows (even though some docs kind of imply that it does) - you can see those two roles mentioned here:
Once one of those roles is granted you'll be able to login to linux using standard ssh clients - the key thing to be aware of here is that the username is the full name from AD and that this name is case sensitive!
so for example if my AAD user is abcDEF123@contoso.com - this exact username has to be used in linux
If i now login using my favourite ssh client i am prompted as normal for username (where i enter the whole AAD identity) , followed by my password - after you type the password and hit enter you get this:
So now navigate to the microsoft devicelogin portal enter the prompted code:
Go back to linux after that and hit enter and you'll be logged in, if the admin role was granted you'll be a member of the admin group which is defined in the sudoers file to be able to do anything using sudo.
Pretty nice - it means i can have a single identity accessing everything and a single point of control - if a user leaves the company i disable the account in on premise AD - this replicates to AAD and disables it there and then no login is possible to any linux machine - no worrying about having to tidy up local accounts.
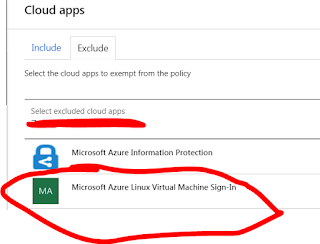
One other thing to mention as it may affect some other implementations of this is that if you have conditional access activated on your AAD then you may need to account for that in the rules defined - in our setup the AADlinux application was not permitted and this was blocking it from working (though we couldn't see that and had to raise a ticket with MS to discover that).
To fix we added an exclusion rule to enable this application to be able to talk to AAD rather than it just being completely blocked - for reference this is what the application is called in case you need to make a similar exclusion
The feature is currently still in preview (but surely must be coming out of that soon) and currently doesn't support all linux flavours - there are more details here from the official MS docs:
https://docs.microsoft.com/en-us/azure/virtual-machines/linux/login-using-aad
Nice job though - this is a real identify and access control improvement.






soooo trying this tomorrow :-)
ReplyDeleteI've been harping on about Linux SSO for moons at our place.
good post dude!
The Best of the Blogs You have Mentioned here.
ReplyDeleteWindows Azure Admin Online Training
Nice and good article.Thanks for sharing your valuable information
ReplyDeleteDevOps Training
DevOps Online Training
I feel really happy to have seen your webpage and look forward to so many more entertaining times reading here. Thanks once more for all the details.
ReplyDeleteDevOps Training in Bangalore | Certification | Online Training Course institute | DevOps Training in Hyderabad | Certification | Online Training Course institute | DevOps Training in Coimbatore | Certification | Online Training Course institute | DevOps Online Training | Certification | Devops Training Online
abinitio online training
ReplyDeletespark training
scala training
sccm training
mysql training
Good post, Thanks for sharing!
ReplyDeleteDevOps Training
DevOps Online Training
OaffiAinsu_1993 Marcus Bradfield https://wakelet.com/wake/0UksFGEEzHvtnbjDuLBdy
ReplyDeletearunitbio
Top Notch article, it is particularly valuable! I unobtrusively began in this, and I'm transforming into more familiar close by inside the focal point of it better! Delights, articulation war more and hauling continuing extraordinary! Card Recovery Software With Key
ReplyDeleteRecuva Free Download Full Version With Crack Howdy, I see as cognizant part concentrating on this text a delight. it's miles really pleasurable to prepared and fascinating and profoundly tons looking take care of to perusing extra of your trademark..
ReplyDeleteHappy Birthday! I feel blessed to have such a loving and caring husband. Happy birthday husband! Thank you for being the reason of my smile. I love you ...Long Distance Birthday Wishes
ReplyDeleteNice Information.Fusion 360 Crack
ReplyDeleteBest Blog.Adobe Premiere Pro Crack
ReplyDeleteThank you for sharing such a clear and insightful piece. I truly found your ideas valuable and engaging. I really appreciate how you connected different industries and perspectives, it gave me a fresh way to think about it.
ReplyDeleteRoot Canal Treatment In Madinaguda
كل الشكر اعمال مميزو زورو اعمال مؤسسة البلد وتعرف علي خدماتنا تسليك مجاري في عجمان الامارات فـ تعد مشكلة انسداد المجاري أحد أكثر المشكلات شيوعًا في المنازل، وقد تؤدي إلى روائح كريهة ومشكلات صحية. هنا تأتي أهمية خدمة تسليك المجاري التي تقدمها "ولاد البلد" تعتمد الشركة على تقنيات حديثة وأدوات متخصصة للتعامل مع هذه المشكلة.
ReplyDelete