So more on this cloud stuff then.....
Well in this case the work is just as applicable to a normal on premises configuration with 'standard' Active directory (other types of ldap directory can be used but i guess AD is the most widespread).
In this particular case (a follow up to my post on configuring HA for cloud control in Azure) i now want to enable single sign on to this cloud control using the PaaS instance of Azure AD i setup - note i absolutely do not want full blown AD to setup and manage - that is way beyond my current skillset.
This post assumes that Azure AD has been provisioned in Azure and you have a domain name something like myfirstgoatthis.onmicrosoft.com (if you are just using AD that your AD guys set up on site then just go with what they did).
In the azure AD management screens in the old portal (this bit does not seem to be in the new portal yet) make sure you enable domain services - this is the bit that adds ldap support - for normal AD you'll get this anyway.
To make this clear - thats this screen
Once all thats in place you need to create an account that will be used to query the directory and validate that the users password is correct.
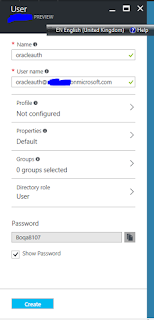
To do that go into the users section on azure ad and add one ( i called mine oracleauth)
Once thats done you have to go and change the password and set up a recovery email - the original password and state of the account is not usable for us yet - so thats this screen when you login to the azure portal using that new login
Now that account is in place we need to tell cloud control we want to enable ad authentication.
I thought this may be available via a gui - it's mentioned in the security console but there is no functionality to change it - as shown here
To enable AD we have to use command line - and to cut a long story short here is that command line
emctl config auth ad -ldap_host your_dns_or_ip_for_domain_services -ldap_port 389 -ldap_principal 'oracleauth@yourdomainhere.onmicrosoft.com' -ldap_credential 'yourpasswordfororacleauthhere' -user_base_dn 'dc=firstbitofyourdomain,dc=onmicrosoft,dc=com' -group_base_dn 'dc=firstbitofyourdomain,dc=onmicrosoft,dc=com' -sysman_pwd yoursysmanpassword
Hopefully thats fairly self explanatory - they are single quotes in the command line - this seems wrong somehow but double quotes don't work and they have to be single.
After you run that you'll see
Oracle Enterprise Manager Cloud Control 13c Release 2
Copyright (c) 1996, 2016 Oracle Corporation. All rights reserved.
Configuring LDAP Authentication ... Started
Successfully validated connection to LDAP server
Configuring LDAP Authentication ... Successful
If this is a multi-OMS environment, restart all OMS(s) using: 'emctl stop oms -all' and 'emctl start oms'
If use_ssl has been specified and the LDAP server certificate is self-signed, as part of the validation process, we have imported it into the keystore configured for Weblogic Server.
then you have to fully stop and start the OMS via
emctl stop oms -all
emctl start oms
Note here that if you have HA OMS setup you have to run the command against both OMS's and you have to make sure the steps are done to both at the same time i.e.
emctl command against both
emctl stop against both
emctl start against both
if you try to just do it against one it won't work (at least not for me)
After thats run the security console now shows this
So looking good lets try adding a user - and straight away we see a new option
Lets add my test account as a check
I give it super admin to be lazy just to prove it and i can see from the summary screen that we are now adding an oracle internet directory account (someone in oracle has a sense of humour - this is of course now an AD account)
If we look at the user screen now we can see it is of different type
So lets try logging in as linuxtest.....
And we're straight in to the accessibility page - as easy as that!
Now the above should be pretty much directly reusable in any Azure AD and cloud control setup - just change the appropriate parts and away you go!










sahuKlig-waBillings Edward Gonzales https://marketplace.visualstudio.com/items?itemName=leoprimexki.Descargar-Enter-Digiton-gratuita-2022
ReplyDeletevretwanelas
planricont-no Juantonio Payton https://www.stavadalenskisenter.com/profile/greenergreenergreener/profile
ReplyDeletewaipanquiprof
cyagnosApel-do Edward Clarke Google Chrome browser
ReplyDeleteMorphVOX Pro
Avast Premier
benmahorar
NputniXardo-Newark Diana Brown This is there
ReplyDeletethere
cobbblacdanre